Interesting historic read of notes on end 1970s Apple SSAFE project – how it started and ended
Posted by jpluimers on 2017/02/27
 This appeared a few days back: [WayBack] http://bitsavers.trailing-edge.com/pdf/apple/ssafe/Apple_SSAFE_Project.pdf
This appeared a few days back: [WayBack] http://bitsavers.trailing-edge.com/pdf/apple/ssafe/Apple_SSAFE_Project.pdf
It’s about “Software and Security from Apple Friends and Enemies” an early exchange of ideas and possibilities for DRM in the Apple ][ and Apple III era.
I got it via my bitsavers.org RSS subscription, but it has been over the net in quite a few other places as well:
- Longer articles:
- [WayBack] applemos Software Security from Apples Friends and Enemies
(which due to my dyslexic - [WayBack] Documents unearthed from early Apple history show shift in company focus from hobbyists to businesses
- [WayBack] Found at a thrift shop: the last record of a doomed Apple DRM effort from 1979 / Boing Boing
- [WayBack] Apple SSAFE Project.pdf (1979) | Hacker News
- [WayBack] Vintage Apple memos refer to dongles as ‘a case of the cure being worse than the disease’ | 9to5Mac
- [WayBack] Treasure Trove of Internal Apple Memos Discovered in Thrift Store
- [WayBack] applemos Software Security from Apples Friends and Enemies
- PDF scans:
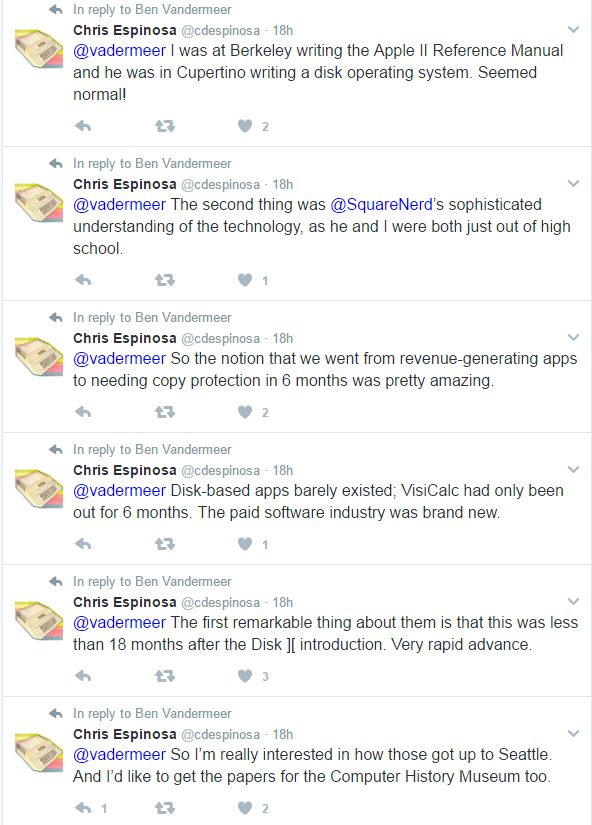
I think the most important quote is from the one on reddit, submitted 20170223 by vadermeer for which I added some WayBack/Archive.is links:
[WayBack] Found Internal Apple Memos about copy protection for Apple II, SARA, LISA(self.VintageApple)
The reddit thread is very nice reading as it explains how close we are now to this Level 1:
Level 1. Totally secure. Absolutely no method of stealing the software. 100% effective. Note that the ideal, level 1, is achievable only through disallowing any access of any kind to the software and the computer. Not very practical in our circumstances.
and this one from boingboing:
It’s so neatly packaged and well-documented it could be a Harvard Business Review case-study.
Edit 20240819: the above Googl links pointed to [Wayback/Archive] Apple SSAFE Project.pdf – Google Drive.
--jeroen






Leave a comment