Archive for the ‘Internet’ Category
Posted by jpluimers on 2026/05/01
Posted in Amazon S3, Amazon.com/.de/.fr/.uk/..., Apple, AWS Amazon Web Services, Cloud, Cloud Apps, GCP Google Cloud Platform, Infrastructure, Internet, Missed Schedule, Power User, SocialMedia, WordPress | Leave a Comment »
Posted by jpluimers on 2026/04/21
Reminder to self: [Wayback/Archive] Hacker Hosting
HackerHosting biedt Hackers, die samenkomen in
hackerspaces, in
hotels en op
campings de mogelijkheid om te genieten van hoge kwaliteit hosting in Nederland, tegen een tarief waarvoor zelfs ‘kippenschuur-hosters’ en ‘brandgevaarlijke-datacenter-hosters’ het niet doen.
Via [Wayback/Archive] Angry Nerds 278 – Corrigendum – YouTube
--jeroern
Posted in Development, Hosting, Internet, ISP, Power User | Leave a Comment »
Posted by jpluimers on 2026/04/10
 I mention dead links a lot, and always try to archive content before scheduling it in a blog post.
I mention dead links a lot, and always try to archive content before scheduling it in a blog post.
No different for [Wayback/Archive] Some URLs Are Immortal, Most Are Ephemeral, which provides background information about how the short lifespan of most URLs.
Their 2024 publication was a poster in PNG and PTTX format (linked below under the abstract), so I created this PDF out of it:
Abstract
Read the rest of this entry »
Posted in Conference Topics, Conferences, Event, Internet, LifeHacker, Power User, Web Browsers, WWW - the World Wide Web of information | Leave a Comment »
Posted by jpluimers on 2026/04/01
For a while now, after initially displaying archived Google Search results, it changes the Wayback Machine archival URL after displaying.
Examples:
https://web.archive.org/web/20230322163526/https://www.google.com/web/20230322163526/https://www.google.com/search?q=excel+last+delimiterhttps://web.archive.org/web/20230321192712/https://www.google.com/search?q=excel+textafter+textbefore+textsplit+site:https:%2F%2Fsupport.microsoft.com%2Fen-us%2Foffice%2F&google_abuse=GOOGLE_ABUSE_EXEMPTION%3DID%3D3020867903a1f6fa:TM%3D1679426832:C%3D%3E:IP%3D207.241.225.236-:S%3DTSrpWMPwWKoNpiXh-oD21Q%3B+path%3D/%3B+domain%3Dgoogle.com%3B+expires%3DTue,+21-Mar-2023+22:27:12+GMThttps://web.archive.org/web/20230321192712/https://www.google.com/web/20230321192712/https://www.google.com/search?q=excel+textafter+textbefore+textsplit+site:https:%2F%2Fsupport.microsoft.com%2Fen-us%2Foffice%2F&google_abuse=GOOGLE_ABUSE_EXEMPTION%3DID%3D3020867903a1f6fa:TM%3D1679426832:C%3D%3E:IP%3D207.241.225.236-:S%3DTSrpWMPwWKoNpiXh-oD21Q%3B+path%3D/%3B+domain%3Dgoogle.com%3B+expires%3DTue,+21-Mar-2023+22:27:12+GMT
I want to write a Bookmarklet that fixes these.
There is not much in the results of
[Wayback/Archive] “GOOGLE_ABUSE_EXEMPTION” “Wayback” – Google Search, but I think this happens when there is a high frequency Google Search archivals from the Wayback Machine.
–jeroen
Posted in Google, GoogleSearch, History, Internet, InternetArchive, Power User, WayBack machine | Leave a Comment »
Posted by jpluimers on 2026/03/30
Het was me al een tijdje opgevallen dat ik nauwelijks meer fysieke post van Movir kreeg.
Ik dacht aan een probleem bij de post, maar het bleek erger:
Toen ik een tijd terug een on-line profiel aangemaakt had ik een PDF van mijn profiel gemaakt zodat ik wist wat er was geregisteerd.
Daarin stond “Communicatievoorkeur Per post”.
Read the rest of this entry »
Posted in About, archive.is / archive.today, Internet, InternetArchive, LifeHacker, Personal, Power User, WayBack machine | Leave a Comment »
Posted by jpluimers on 2026/03/04
Dit is net zo nalatig als de Odildo hack waar alle klantgegevens mee op straat kwamen te liggen: [Wayback/Archive] Odido-router verzamelt analytics van je huishouden
Bevindingen in het kort
- De Odido-router haalt bij een nieuwe WAN-verbinding een bash-script op over een onversleutelde HTTP-verbinding.
- Je kan dit script manipuleren om een root shell op je router te krijgen.
- Als je TLS-verkeer mitm’t zie je analytics-data over de lijn gaan; de scripters hebben TLS-validatie uitgezet (`curl -k`) dus je kan dit ‘versleutelde’ analytics-verkeer inzien.
- Je router stuurt namen en MAC-adressen van devices in je huis door naar Lifemote. Verder deelt het ding de SSID’s en MAC-adressen van WiFi-netwerken in de buurt. En wat analytics-stats over je dataverbruik. Lifemote adverteert met “AI-Powered Home Wi-Fi Solutions for ISPs”. Het voelt wat vies dat zij AI’s gaan trainen met data uit mijn huishouden. Daar vind ik wat van.
--jeroen
Posted in *nix, *nix-tools, bash, bash, Development, ISP, Odido (ex Dutch T-Mobile), Power User, Python, Scripting, Software Development | Leave a Comment »
Posted by jpluimers on 2026/02/26
The description of [Wayback/Archive] GitHub – dessant/web-archives: Browser extension for viewing archived and cached versions of web pages, available for Chrome, Edge and Safari is missing Firefox and Opera, but in the meantime the extension is available in these stores for:
As a great example of how to write a browser plugin for all these architectures, it shows how to write this in mostly JavaScript with Vue.js with a tiny bit of play HTML.
Web Archives is a plugin that lets you search either the URL from the current browser tab, or a URL you type, within various archival sites (all Wikipedia links):
Read the rest of this entry »
Posted in Archive Today controversy, archive.is / archive.today, Archiving, Chrome, Development, Edge, Firefox, Internet, InternetArchive, Opera, Power User, Safari, Software Development, WayBack machine, Web Browsers, Web Development | Leave a Comment »
Posted by jpluimers on 2026/02/24
LLM eat a lot of energy and are their hallucination are bad: [Wayback/Archive] LLM-generated passwords ‘fundamentally weak,’ experts say • The Register
Your AI-generated password isn’t random, it just looks that way
…
AI security company Irregular looked at Claude, ChatGPT, and Gemini, and found all three GenAI tools put forward seemingly strong passwords that were, in fact, easily guessable.
…
Basically they are almost as good as the 2007 XKCD “four” number generator, the 2013 XKCD “I’m So Random” or the 2001 Dilbert “nine” number generator further below (don’t read the latter if you dislike Scott Adams)
Is it a coincidence or are these two using two small squared numbers?
Anyway: avoid LLM whenever possible, as most often they do more bad than good.
And for passwords, better use the blog post that was already scheduled for tomorrow: Generating random strings for passwords and uuids/guids on both Windows and Linux using base64 and hex encoding, plus: “Hive Systems: Are Your Passwords in the Green?”
Via [Wayback/Archive] Eloy.: “LLMs are centrist randomness: not useful for anything that requires truth but neither for password generation” – HSNL Social
Below this post, there are some great responses as well.
Comics
Read the rest of this entry »
Posted in AI and ML; Artificial Intelligence & Machine Learning, C++, Conference Topics, Conferences, Development, Event, Internet, InternetArchive, LLM, Pingback, Power User, Python, Scripting, Software Development, Stackoverflow, WayBack machine | Leave a Comment »
Posted by jpluimers on 2026/02/23
I pulled this post forward from the blog queue in light of the recent Archive Today controversy (which started because of the Gyrovague article mentioned below). Please note that in this controversy, the Wayback Machine of the Internet Archive plays no role: it is purely about the Archive Today behaviour. Apart from this remark above the line I left this blog post in the original form I wrote it in, as I liked it a lot and quite a few published and queued blog posts still depend on it.
From a while back, but still a historic relevant article: [Wayback/Archive] archive.today: On the trail of the mysterious guerrilla archivist of the Internet – Gyrovague
Via [Wayback/Archive] difference between archive today and wayback machine – Google Search
Related:
Read the rest of this entry »
Posted in Archive Today controversy, archive.is / archive.today, Archiving, Bookmarklet, History, Internet, mementoweb, Power User, WayBack machine, Webcitation | Leave a Comment »
Posted by jpluimers on 2026/02/12
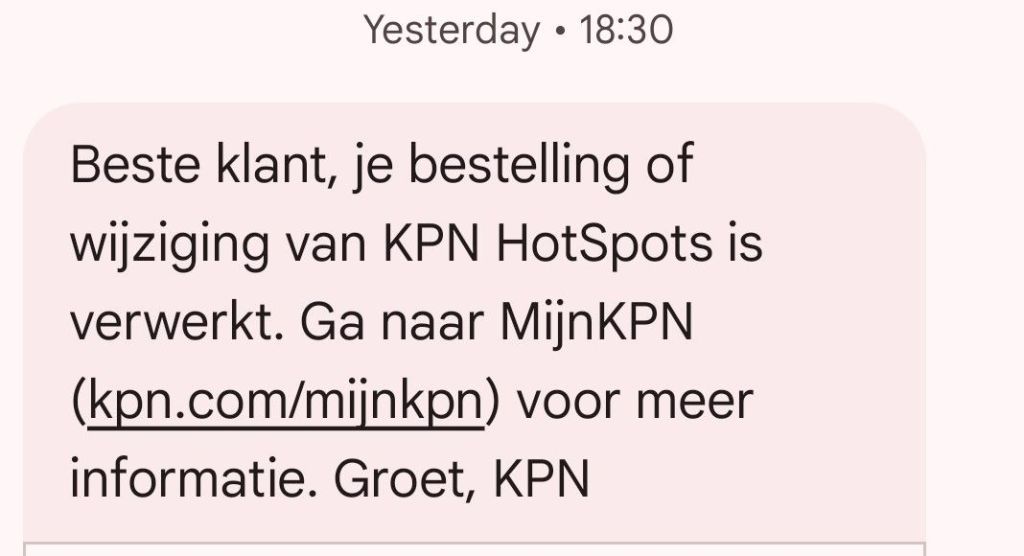
De SMS van dinsdag:
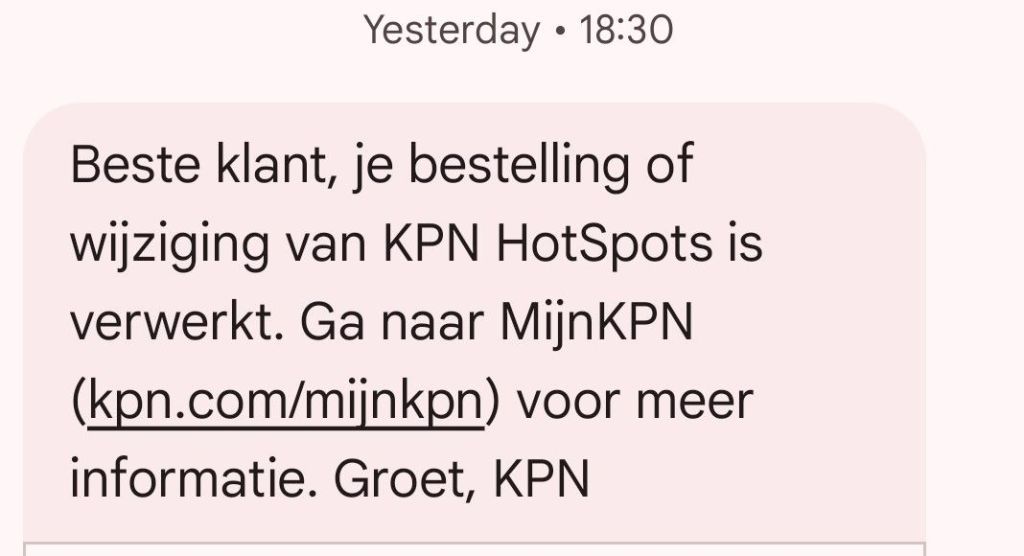
Beste klant, je bestelling of wijziging van KPN HotSpots is verwerkt. Ga naar MijnKPN (kpn.com/mijnkpn) voor meer informatie. Groet, KPN
Die SMS had nooit verzonden moeten worden, want KPN HotSpots zijn al jaren gratis voor iedereen toegankelijk, en de abonnee had zelf niets gewijzigd.
Zie: [Wayback/Archive] SMS gehad dat wijziging van KPN Hotspots is verwerkt | KPN Community
Woensdag kwamen er, ook per SMS, excuses. Twee keer zelfs.
Read the rest of this entry »
Posted in Internet, ISP, KPN, Power User | Leave a Comment »






 I mention dead links a lot, and always try to archive content before scheduling it in a blog post.
I mention dead links a lot, and always try to archive content before scheduling it in a blog post.