Archive for the ‘Security’ Category
Posted by jpluimers on 2020/01/31
 Nothing lasts, so the company behind the U2F key on the right is long gone, but their site is archived in Archive.is and the WayBack machine. Since the U2F protocol is open, you can still set up the device and use it. Here is how for your Google account (for instance with GMail), it works in a similar way for other providers:
Nothing lasts, so the company behind the U2F key on the right is long gone, but their site is archived in Archive.is and the WayBack machine. Since the U2F protocol is open, you can still set up the device and use it. Here is how for your Google account (for instance with GMail), it works in a similar way for other providers:
Archived links:
Some of their videos are also still online (embedded links at the bottom of the post):
U2F (or Universal 2nd Factor – Wikipedia) has an open protocol by FIDO Alliance – Wikipedia. More on that in these links below.
One final odd note:
The FIDO alliance still listed Happlink on their web-site when I wrote this blog post.

It used to be at this address: Happlink, 4 rue Jehan Le Povrmoyne, 76240 Le Mesnil-Esnard, France
Read the rest of this entry »
Posted in Power User, Security, U2F FIDO Security Keys | Leave a Comment »
Posted by jpluimers on 2020/01/24
A simple tip on the certbot command-line from [WayBack] User Guide — Certbot 0.19.0.dev0 documentation – Managing certificates (Automatically enable HTTPS on your website with EFF’s Certbot, deploying Let’s Encrypt certificates.):
To view a list of the certificates Certbot knows about, run the certificates subcommand:
certbot certificates
This returns information in the following format:
Found the following certs:
Certificate Name: example.com
Domains: example.com, www.example.com
Expiry Date: 2017-02-19 19:53:00+00:00 (VALID: 30 days)
Certificate Path: /etc/letsencrypt/live/example.com/fullchain.pem
Private Key Path: /etc/letsencrypt/live/example.com/privkey.pem
Via: [WayBack] It there a command to show how many days certificate you have? – Server – Let’s Encrypt Community Support
–jeroen
Posted in Encryption, Let's Encrypt (letsencrypt/certbot), Power User, Security | Leave a Comment »
Posted by jpluimers on 2020/01/14
Below is one of the reasons I try to stay on the back-end side of things. Those are complex enough to focus on for me.
[WayBack] I’m harvesting credit card numbers and passwords from your site. Here’s how.
It basically comes down to:
- anything in the same page has access to anything happening on that page.
- be careful when using
npm and ad networks.
- perform security operations in a light-weight iframe that is scrutinized.
The source of any npm package might be different from the source you find in a the underlying repository. This recursively holds for all the other npmit pulls in.
–jeroen
via: [WayBack] Jeroen Wiert Pluimers – Google+
Posted in Development, Power User, Security, Software Development, Web Development | Leave a Comment »
Posted by jpluimers on 2019/12/31
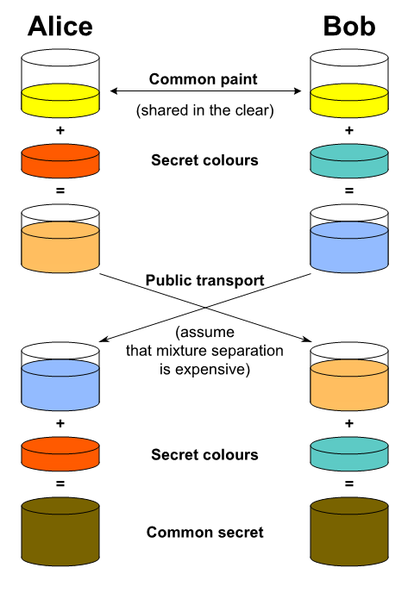
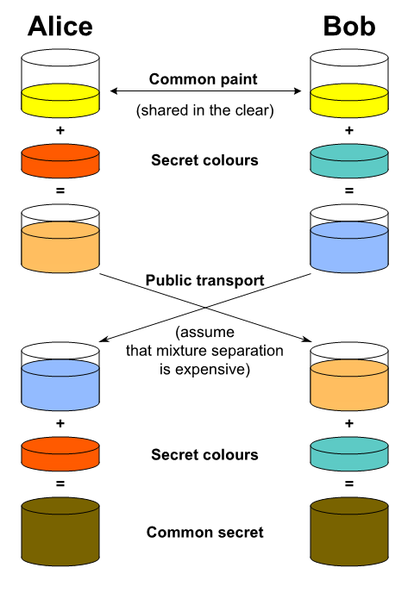 Sometimes a picture or video is better than a thousand words.
Sometimes a picture or video is better than a thousand words.
I wish that back when I learned about the mathematics of the Diffie–Hellman key exchange – Wikipedia
I had seen the picture on the right from File:Diffie-Hellman Key Exchange-modified.png – Wikipedia (via DHKE General overview) which inspired the Computerphile and Art-Of-The-Problem videos below doing the same dynamically with colorised liquids and paint.
Art-Of-The-Problem has a similar video on RSA as well which is also below.
Usually Diffie-Hellman is combined with RSA to prevent man-in-the-middle and allow for perfect forward secrecy. That’s what the final computerphile video is about.
Excellent!
Finally, Computerphile also posted a video with the mathematics. If you’re into that: nice work too!
Via:
–jeroen
Read the rest of this entry »
Posted in Development, Encryption, Power User, Security, Software Development | Leave a Comment »
Posted by jpluimers on 2019/12/27
On my list of things to try:
Tim Berners-Lee, inventor of the World Wide Web, launches Inrupt, a start-up that will take the Solid open source platform and “Solid movement” to the next level with the backing of Glasswing Ventures. A look at the what and why.
For now, I have two WebIds and need to figure out how to link them (:
Hopefully the video below will help with that.
–jeroen
Read the rest of this entry »
Posted in GDPR/DS-GVO/AVG, LifeHacker, Power User, Privacy, Security | Leave a Comment »
Posted by jpluimers on 2019/12/16
Great tip from: [Archive.is] Michal Špaček on Twitter: “Friendly reminder: if you allow users to register email addresses on your domain, make sure they can’t get: admin@ administrator@ hostmaste… https://t.co/wUHXrQC2J0”:
Friendly reminder: if you allow users to register email addresses on your domain, make sure they can’t get:
- admin@
- administrator@
- hostmaster@
- postmaster@
- webmaster@ (and others from RFC 2142)
otherwise users might be able to get an HTTPS certificate for your domain.
–jeroen
Read the rest of this entry »
Posted in Encryption, https, Let's Encrypt (letsencrypt/certbot), Power User, Security | Leave a Comment »
Posted by jpluimers on 2019/10/25
If you find out bookmarklets like the [WayBack] Press-This or [Archive.is] SubToMe do not work on some pages but to on others.
Often it’s not the bookmarklet, but a combination the site disabling CSP (Content Security Policy) and browsers not coping well with that, see for instance:
via:
Read the rest of this entry »
Posted in Bookmarklet, CSP, Power User, Security, Web Browsers | Leave a Comment »
Posted by jpluimers on 2019/09/27
So I won’t forget; the steps below based on and assumes ~/Versioned is the directory where you keep repositories in:
# cd ~/Versioned
# git clone https://github.com/certbot/certbot.git
...
# cd certbot
# git fetch --all
Fetching origin
# git checkout alt_override
Branch 'alt_override' set up to track remote branch 'alt_override' from 'origin'.
Switched to a new branch 'alt_override'
# ./certbot-auto --os-packages-only
OS packages installed.
# ./tools/venv.sh
... very long log ...
Please run the following command to activate developer environment:
source venv/bin/activate
# source ./venv/bin/activate
[venv] # venv/bin/certbot renew --force-renewal
–jeroen
Posted in Encryption, Let's Encrypt (letsencrypt/certbot), Power User, Security | Leave a Comment »
 Nothing lasts, so the company behind the U2F key on the right is long gone, but their site is archived in Archive.is and the WayBack machine. Since the U2F protocol is open, you can still set up the device and use it. Here is how for your Google account (for instance with GMail), it works in a similar way for other providers:
Nothing lasts, so the company behind the U2F key on the right is long gone, but their site is archived in Archive.is and the WayBack machine. Since the U2F protocol is open, you can still set up the device and use it. Here is how for your Google account (for instance with GMail), it works in a similar way for other providers: