Having it accidentally made it to the CBL (Composite Blocking List – Wikipedia) a long time ago, I discovered the page started with (WayBack link mine):
IMPORTANT: Many CBL/XBL listings are caused by a vulnerability in Mikrotik routers. If you have a Mikrotik router, please check out the [WayBack] Mikrotik blog on this subject and follow the instructions before attempting to remove your CBL listing.
It wasn’t one of my Mikrotik devices, as first of all they had all being patched out of the box from a really empty internal network before being externally exposed to the internet or more busy internal networks, and second because the CBL entry was a one off on one specific day where someone used our guest network.
Some CBL entries in the range where it was displayed, quite a while after CVE-2018-14847 became public:
If you want to try for yourself or harden it: [WayBack] Exploiting Mikrotik for Good ? | Syed Jahanzaib Personal Blog to Share Knowledge !
So I did some more digging.
First of all, it seems that if you ever had an infected Mikrotik system, then you have to factory reset it, then upgrade and configure from scratch. Otherwise at least the SOCKS and Web proxy services can still send out spam: [Archive.is] spammer behind mikrotik or mikrotik is the spammer : sysadmin. There, the best advice was
Your mikrotik has been compromised then, I would suggest either going on site and rebuilding the router from scratch, or looking at a few things:
-
Check System -> Scheduler for any schedules running( that you haven’t configured yourself)
-
Check Systems -> scripts for any installed scripts that are running and delete, also look for running jobs and terminate them.
-
Finally check the file explorer for any suspicious files or scripts, and delete any you find. A default library should look like this: flash (the partition) -pub -skins anything else that you havent put there yourself, Delete.
Anything else that I have mentioned above should be empty. Also you need to re-evaluate the security of your network. If you happen to be on site, reset the router and remove the default configuration on the boot prompt. Create two rules:
-
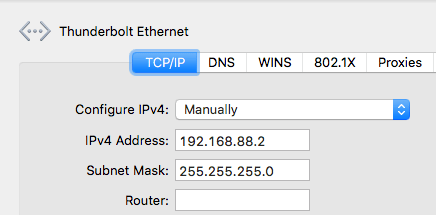
Allow input chain source IP from your default local network, if i remember correctly its 192.168.88.0/24
-
create an explicit drop rule on input chain for all interfaces and addresses + ports
-
disable IP – services except winbox Finally work your way up on what your network needs step by step by creating rules to accept traffic. And be sure to put your explicit rule on the bottom of the list by drag-and-dropping. That is all I can say, I hope I could be of help.
This means the advice in these two links might not be enough:
Another helpful resource [WayBack] Router Sending Spam – MikroTik which discusses the firewall rules, socks and web proxy services.
Second, there are a truckload of these devices around: [WayBack] Thousands of Compromised MikroTik Routers Send Traffic to Attackers and [WayBack] Thousands of MikroTik routers are snooping on user traffic | ZDNet write that in September 2018, at least 7500 devices were known infected and about 370-thousand endpoints vulnerable.
Third, you should be able to use [WayBack] Manual:Tools/Netwatch – MikroTik Wiki to check if you are on the CBL: [WayBack] Probing CBL blacklist – MikroTik.
Read the rest of this entry »