[Wayback] Valetudo | Cloud-free control webinterface for vacuum robots
Valetudo is a standalone binary which runs on rooted Vacuums of the Xiaomi ecosystem and aims to enable the user to operate the robot vacuum without any Cloud Connection whatsoever.
You can even use it to make a WiFi heat map of the floors in your home: the Valeroni app can do that for you.
The Valeroni app is open source too: [Wayback/Archive.is] ccoors/Valeronoi: A WiFi mapping companion app for Valetudo
Via [Archive.is] Kristian Köhntopp on Twitter: “Paging @sys_adm_ama: … Alternative Firmware für Robot-Staubsauger … Alternative Firmware für Robot-Staubsauger verwenden, um das Wifi im Haus zu mappen (und Staub zu saugen)”
–jeroen








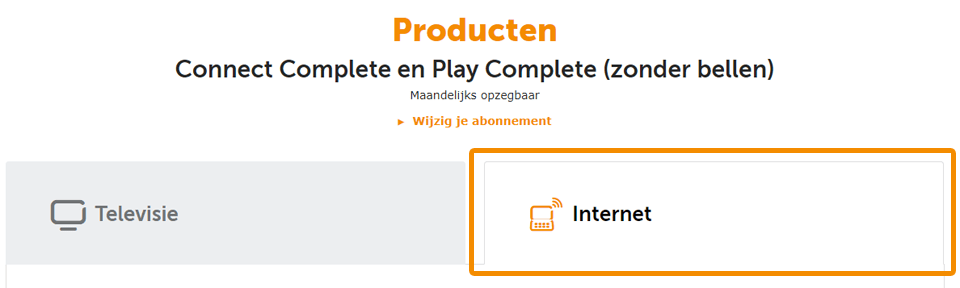
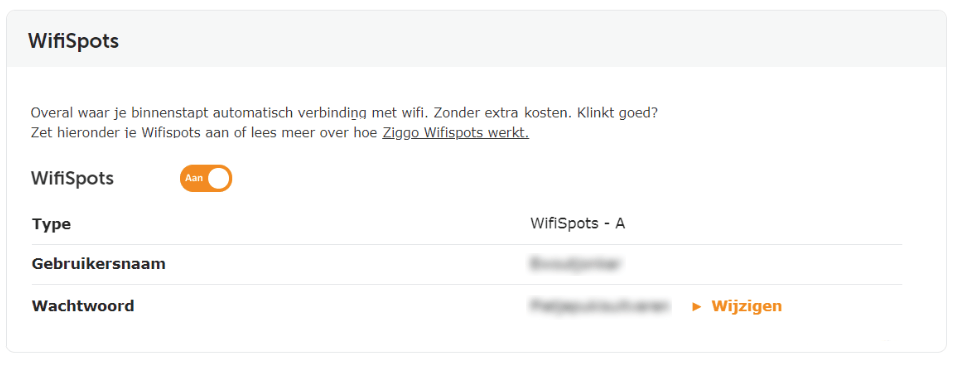
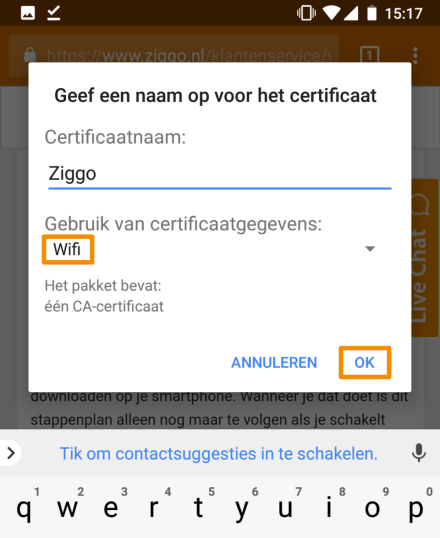
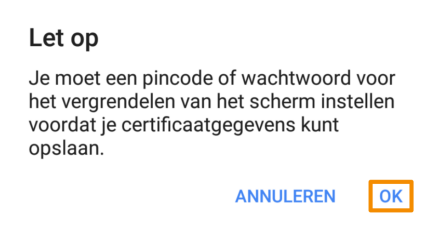
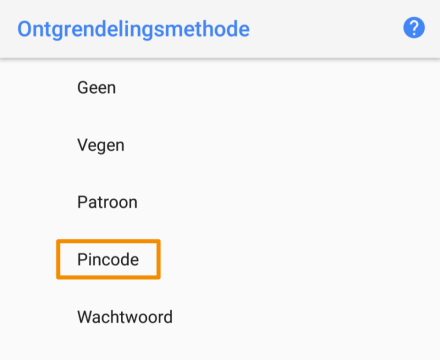
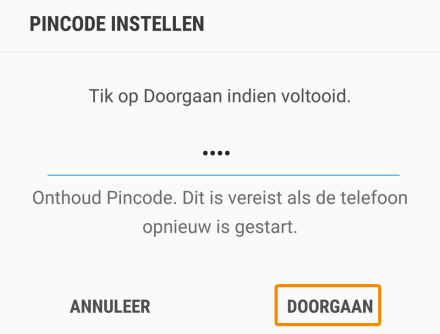
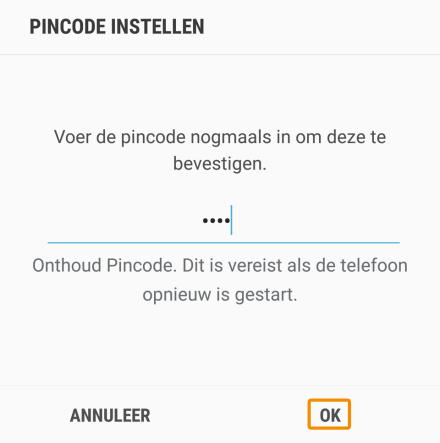
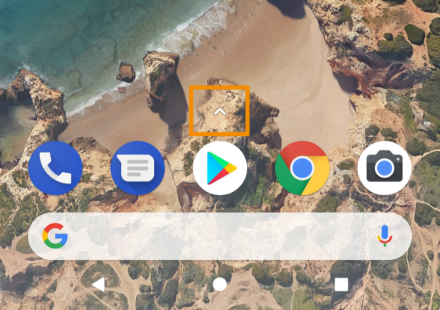
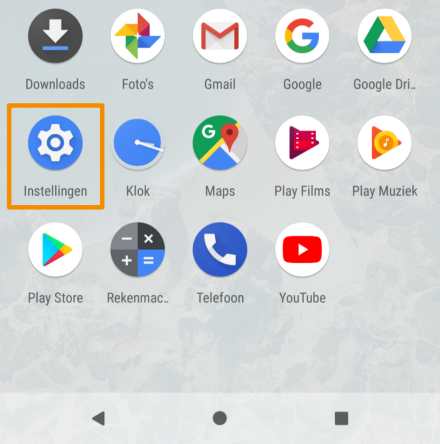
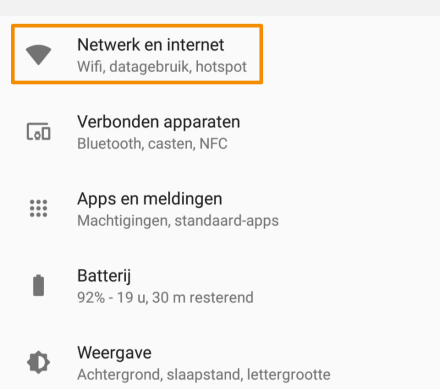
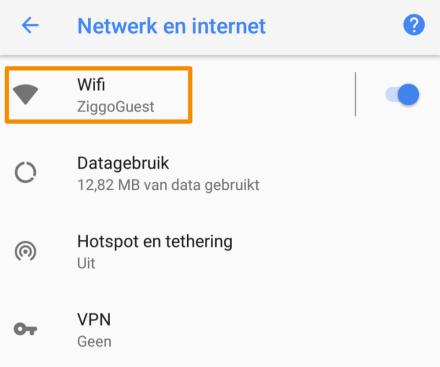
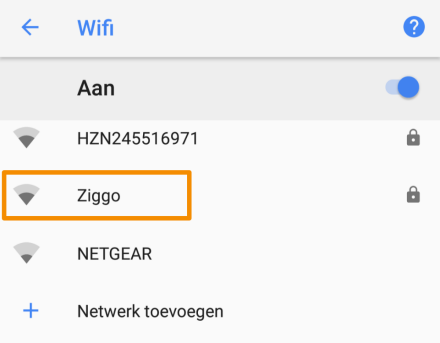
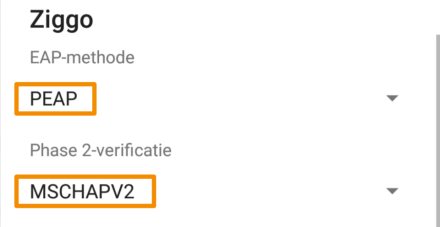
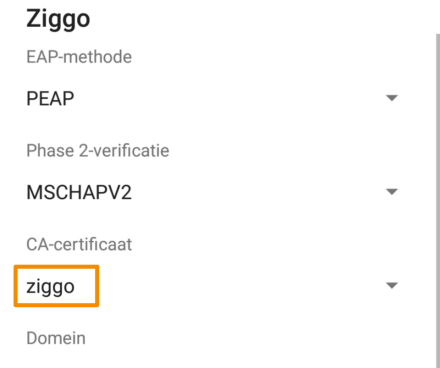
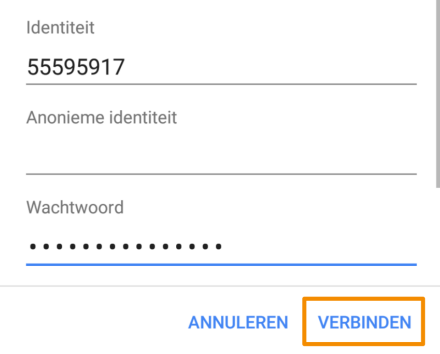
 Het zijn behoorlijk veel stappen, maar de meeste klanten hebben in 10 minuten Wifispots ingesteld.
Het zijn behoorlijk veel stappen, maar de meeste klanten hebben in 10 minuten Wifispots ingesteld.