A while back, while using “git svn”, on a Windows system, I got [Archive.is] “error: invalid object 100644” “git svn” – Google Search after statements like this:
# git svn rebase
error: refs/remotes/git-svn does not point to a valid object!
error: invalid object 100644 ac7df132f5bd7d639fc525f1f0204a546658d0c5 for 'Source/ToDoList/GX_ToDo.pas'
fatal: git-write-tree: error building trees
write-tree: command returned error: 128
# git svn fetch
error: refs/remotes/git-svn does not point to a valid object!
error: invalid object 100644 ac7df132f5bd7d639fc525f1f0204a546658d0c5 for 'Source/ToDoList/GX_ToDo.pas'
fatal: git-write-tree: error building trees
write-tree: command returned error: 128
In my case, regular git operations (like branching, committing, pushing, etc) worked fine, but git svn would fail.
One problem was that [Archive.is] “error: refs/remotes/git-svn does not point to a valid object” – Google Search only returned one un-meaningful result: [WayBack] gist:87613 · GitHub.
Luckily, I had a backup (though it was from a while ago as that VM had not been in use for quite some time) which is the first part in [WayBack] Git FAQ – Git SCM Wiki: How to fix a broken repo?.
Since I was still interested finding out how to resurrect, just in case this happens at a time the backups do not go back far enough, I tried the steps below.
The very first fixing step is to ensure you can quickly restore things, or even better: operate on a copy of the broken pieces. On Windows, robocopy /mir is my friend for this, in Linux rsync -avloz (although on some systems, -z crashes).
TL;DR from the fixing steps
Find out what problems you have, and in which order to fix them. Otherwise you will break more stuff and take longer to fix it.
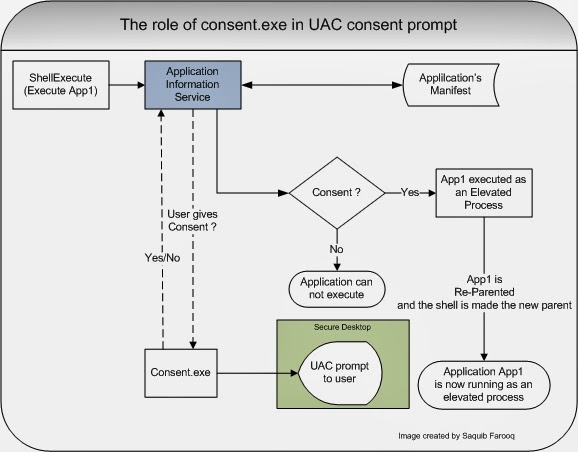
In this case, two things failed: one on the git side, and one on the git svn side. Since git svn depends on git, the best approach is to fix the git problem first, then the git svn thing.
Fixing this manually try 1
Read the rest of this entry »