Archive for the ‘Security’ Category
Posted by jpluimers on 2016/11/18
Security always has the human factor involved which means that we screw up like here:
Source: [WayBack] If you are a KDE neon user, reinstall your distro now! | CIO
A little blunder was committed by the core developers that made the entire archive insecure:
“Best practice when setting that up is to use the trusted SSH protocol to open a tunnel and upload through that,” said Riddell, “Unfortunately in setting up that new archive I had it listening for uploads on the whole network not just the local SSH tunnel.”
–jeroen
via: [WayBack] hmmm – looks legithttp://www.cio.com/article/3142789/linux/if-you-are-a-kde-neon-user-reinstall-your-distro-now.html – Joe C. Hecht – Google+
Posted in Power User, Security | Leave a Comment »
Posted by jpluimers on 2016/10/28
I’m really glad that more and more suppliers are providing sha hashes for their downloads.
It allows you to verify an already downloaded binary is in fact
For instance, Cisco does this with their Jabber Messaging software. That way I could verify the (when I wrote this) most recent versions were indeed the ones I already had by just clicking on the filename (no need to click on the Download button).
- Mac:
- $ shasum -a 512 CiscoJabberMac-11.0.0.216341.zipbd03b0f8542e0244b30601647e991eec74c2e5b358bf68cdf1b4d6f4e62f96fed83f813d0033e696012dc320a80cc96b9c17d5f98250d44b5252c06732c16df5 CiscoJabberMac-11.0.0.216341.zip
- Windows:
- $ shasum -a 512 CiscoJabber-Install-ffr.11-0-1.zip
7335b739498ca365952325931709bae1c0f5916302117b75fc06862d5623a017834ef3f6fafe76feb722dca5618c1e2d11be17e739a59e0b76a3c382f6d9c31b CiscoJabber-Install-ffr.11-0-1.zip
–jeroen
Posted in Hashing, Power User, Security | Leave a Comment »
Posted by jpluimers on 2016/10/24
This Plain Text Offenders site lists email screenshots of organisations sending back plain-text passwords they kept on file (According to Robert Love, Idera/Embarcadero should be on the list as well).
It is one of the most horrible things that can be done for a password.
Business and IT do many horrible things, so I really hope someone will start a similar site about SSL Labs F-rated domains. The ones that are so broken that they degraded their https to virtually plain-text http quality.
In the past, a notorious example of this was Embarcadero, who in the past managed to get F-rating or had wrong configurations on the below domains, therefore preventing me from logging in and getting new products from them (which is far worse than them not cleaning up their bug database):
Read the rest of this entry »
Posted in Delphi, Development, Hashing, https, OpenSSL, Power User, Public Key Cryptography, QC, Security, Signing, Software Development | 3 Comments »
Posted by jpluimers on 2016/10/13
IRC #letsencrypt-dev today:
wiert
Is there any way for `certbot-auto` to show for which domains/apache-configs it has certificates?
pdeee
wiert, we actually made a ticket for 0.10.0 to do that
https://github.com/certbot/certbot/issues/3615
in the mean time, your imperfect options are:
for file in /etc/letsencrypt/live/*/fullchain.pem ; do echo -n $file ; openssl x509 -text -noout -in $file | grep DNS; done
for installation in Apache configs, you can follow that with:
grep /etc/letsencrypt/live /etc/apache2/sites-enabled/*
wiert
@pdeee on OpenSuSE, the last statement should be
grep -r /etc/letsencrypt/live /etc/apache2/*
–jeroen
Posted in *nix, Encryption, Let's Encrypt (letsencrypt/certbot), Linux, openSuSE, Power User, Security, SuSE Linux | Leave a Comment »
Posted by jpluimers on 2016/09/26
Posted in https, Security | Leave a Comment »
Posted by jpluimers on 2016/09/23
 HTTPSWatch tracks the HTTPS support of prominent websites.
HTTPSWatch tracks the HTTPS support of prominent websites.
Source: HTTPSWatch | Global
Like on the right side.
https isn’t everywhere yet, but growing.
–jeroen
Posted in https, Power User, Security | Leave a Comment »
Posted by jpluimers on 2016/09/23
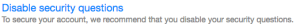
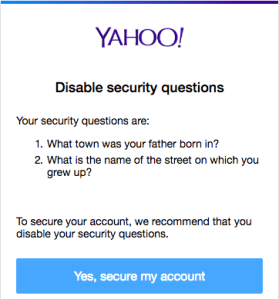
 Steps to disable the security questions in Yahoo:
Steps to disable the security questions in Yahoo:
- Logon at https://login.yahoo.com
- At the top right, click on your name, hover over your name and click “Account Info” to get to Personal Info – Yahoo Account Settings – https://login.yahoo.com/account/personalinfo
- On the left menu, click on “Account Security”.
- Click “Disable security questions”.
Disable security questions – yahoo thinks they’re a bad idea anyway
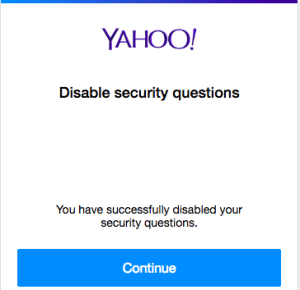
- In the dialog, click “Yes, secure my account”
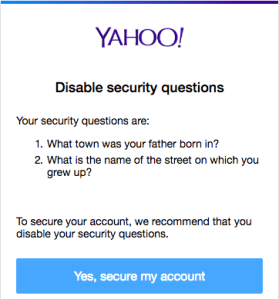
- In the next dialog, click “Close”
- Then verify your other security options (like phone/email recovery and two-factor logon) to enhance your security even more.
–jeroen
Posted in Power User, Security | Leave a Comment »
Posted by jpluimers on 2016/08/29
The canonical answer on extensions and formats like csr, pem, key, pkcs12, pfx, p12, der, cet, cer, crt, p7b, crl, PEM, PKCS7, PKCS12, PKCS10, DER, text, binary, ASN1: certificate – What is a Pem file and how does it differ from other OpenSSL Generated Key File Formats? – Server Fault.
Oh and it contains some openssl conversion tips as well, though this link has more: DER vs. CRT vs. CER vs. PEM Certificates and How To Convert Them.
–jeroen
Posted in Encryption, OpenSSL, Power User, Security | Leave a Comment »
Posted by jpluimers on 2016/08/26
There are quite a few pages on Webserver Cypher Hardening. This is yet another one born because I didn’t know how to compare these lists and why they were so different.
Apparently, OpenSSL has various ways of naming (groups of) cyphers. OpenSSL also disregards any cyphers it doesn’t have.
Basically there are two far ends for cypher lists:
- Fully name all cyphers and their order: long list fine grained control
- Name groups including group order and let OpenSSL expand the groups: short list but coarse grained control.
A way to compere them using openssl ciphers -V is answered at ssl – Hardening web server cyphers: which cypher list to choose, or how to map between Mozilla and Hynek – Server Fault.
Some of the cypher lists I found:
There are two great SSL tests I found out. The first one is online, the second one from the shell.
- SSL Labs:
- shell based SSL/TLS tester: testssl.sh.
–jeroen
Posted in *nix, OpenSSL, Power User, Security | Leave a Comment »
Posted by jpluimers on 2016/08/17
A while ago, testssl.sh [WayBack] needed Darwin binaries (for OS X): Supply Darwin binaries + install documentation · Issue #127 · drwetter/testssl.sh [WayBack]
So I created the small Bourne shell (sh) script below to deliver them.
It allows me to update these gists:
The build script itself is in a gist as well: https://gist.github.com/f4de3937630b87753133.git [WayBack]
It helped me to contribute to these testssl.sh issues:
Not all of these binaries are in https://github.com/drwetter/testssl.sh/tree/master/bin [WayBack] as it makes the testssl.sh repository too bloated. Some (including non-OSX builds made by others) are here:
Eventually the script might get merged into https://github.com/drwetter/testssl.sh/blob/master/utils/make-openssl.sh [WayBack] as there is a Darwin switch in this commit: https://github.com/drwetter/testssl.sh/commit/6efc3e90f52e5926b0853d3b2fb221b631dcf452 [WayBack]
Read the rest of this entry »
Posted in Apple, Development, Mac, Mac OS X / OS X / MacOS, Mac OS X 10.4 Tiger, Mac OS X 10.5 Leopard, Mac OS X 10.6 Snow Leopard, Mac OS X 10.7 Lion, MacBook, MacBook Retina, MacBook-Air, MacBook-Pro, MacMini, OpenSSL, OS X 10.10 Yosemite, OS X 10.8 Mountain Lion, OS X 10.9 Mavericks, Power User, Security, Software Development, xCode/Mac/iPad/iPhone/iOS/cocoa | Leave a Comment »