Ook vandaag even een herinnering aan de NLUUG voorjaarsconferentie 2026 van (komende) donderdag 7 2026 mei in het Van der Valk Hotel Utrecht¹.
Deze keer omdat een goede vriend van me daar spreekt. Arjen Lentz heeft het over A Wizard’s Guide to Foreseeing the Unseen.
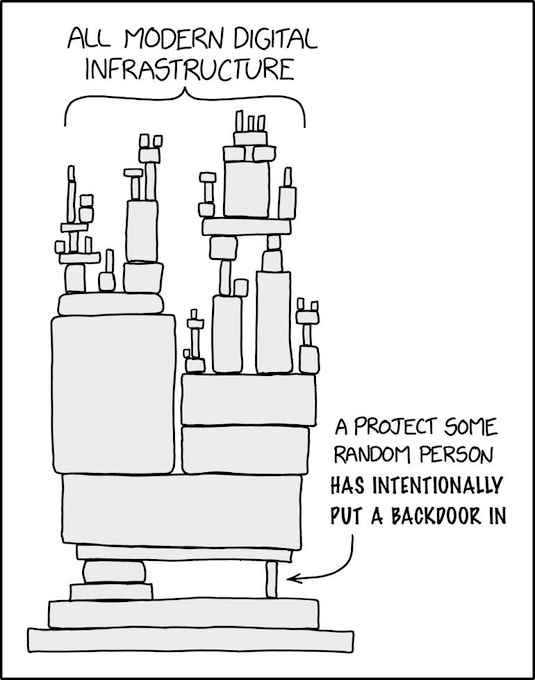
Dat klinkt misschien vaag, het concrete resultaat is dat je met analyse van CVE’s veel te weten komt over hun echte root cause. Die blijkt verrassend voorspelbaar, is fixbaar, en kennis daarover is niet alleen nuttig voor adversaries. Het kan jou namelijk helpen bij de development en selectie van wat je zelf gebruikt.
Het volledige programma staat hieronder², eerst de aankondiging van [Wayback/Archive] L⭕️rd Quux RCX CCX: “Over een week is het zover! De enige NLUUG conferentie van 2026. …” – Mastodon