I an with [Wayback] Craig Buckler to consider Dark Patterns being wider than the strict sense.
For me anything that costs a user extra time or makes accessibility harder is a Dark Pattern.
So I agree with the issues he explains at [Wayback] The Web’s Most Annoying Dark Patterns – SitePoint
Does the web delight or displease you? Craig lists his least favourite UI and marketing dark patterns. Have you developed on the dark side?

Paste is enabled, but does not function
A while ago, I got into one myself. Let me explain.
Having had RSI, I’m dependent on keeping my hands and arms in good shape. This means minimising the use of pointing devices and also trying to minimise typing.
In addition, I have heavily segmented my use of email addresses (among others for cutting down SPAM). Basically any point of contact gets a new email address.
This means I realy on tooling like password managers and email address generators. It means copying and pasting information.
So I bumped into a web-site that disallowed pasting the (unique and long!) email address into the email verification field.
[Archive.is] Jeroen Wiert Pluimers on Twitter: “The @olvg #mijnOLVG site is now on my Dark Patterns list as they make #accessibility harder by blocking pasting into the email address verification field. Blocking the paste-blocker. CC some people advocating mijnolvg.nl @MauricevdBosch @ronklitsie63 @kyntha”
Despite the popup menu, paste didn’t work. Chrome autofill did, but didn’t have the information for this particular (new and unique) email address yet, so could not be used yet.
Disabling the paste block
It is relatively easy to disable a paste block. In this case, I was using chrome, but this can be done with any browser. Some browsers even have optional extensions that can do this for you.
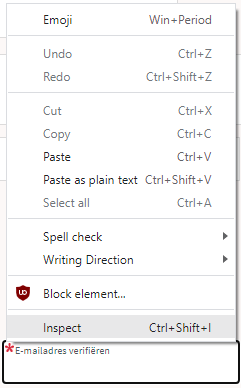
In the case of Chrome, when right clicking, there is an “Inspect” option
Inspect is enabled and actually works.
It inspects the current element, which on this site looks like this:
The element does not contain event handlers. But the code hooks them behind our backs.
On the “Event Listeners” tab on the right, you can see there are two JavaScript methods hooked to the paste handler:
The paste handlers. The first is OK, the second blocks paste.
The first one is OK, though I did not really look into what the proxy does.
Second paste event handler: remove this one.
First paste event handler: keep this one.
The second is not OK, as it effectively prevents the event from being handled any further at all by calling preventDefault
Second paste event handler: remove this one.
- [Wayback] Event.preventDefault() – Web APIs | MDN
The Event interface’s preventDefault() method tells the user agent that if the event does not get explicitly handled, its default action should not be taken as it normally would be.
By clicking on the second Remove button above, the paste blocker is gone and you can paste again.
–jeroen