[WayBack] Uptime Robot on Twitter: “Sorry all that the API and status pages fluctuated since the last 18 hours. The issue is completely fixed and it is all back to normal now.”
[WayBack] Jeroen Pluimerson Twitter: “Some are still broken, especially the ones with IDs 778601760 778601763 778601765 778601777 778601814 779973649 779677530 779677532 All of them reachable through various ISPs, but UpTimeRobot marks them down since about 11 hours”
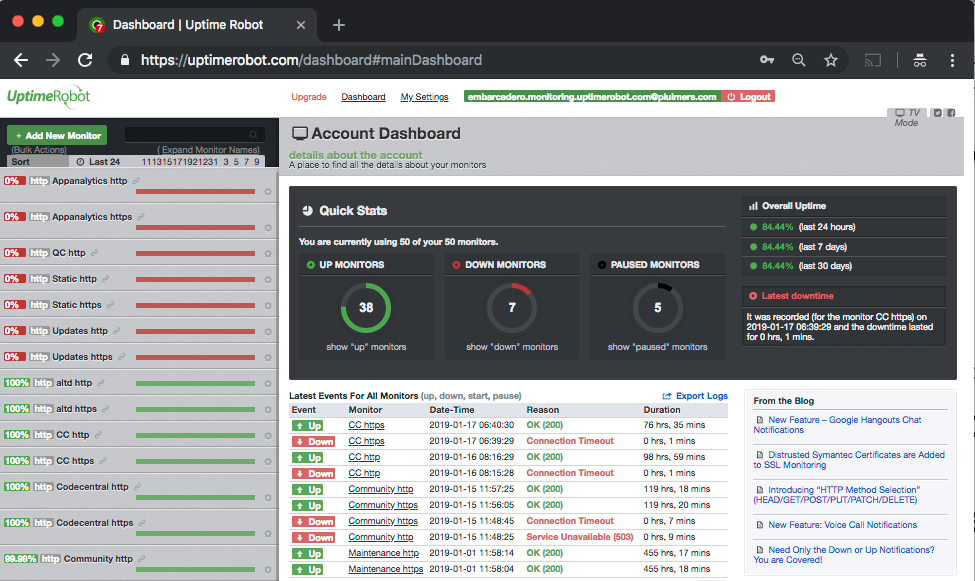
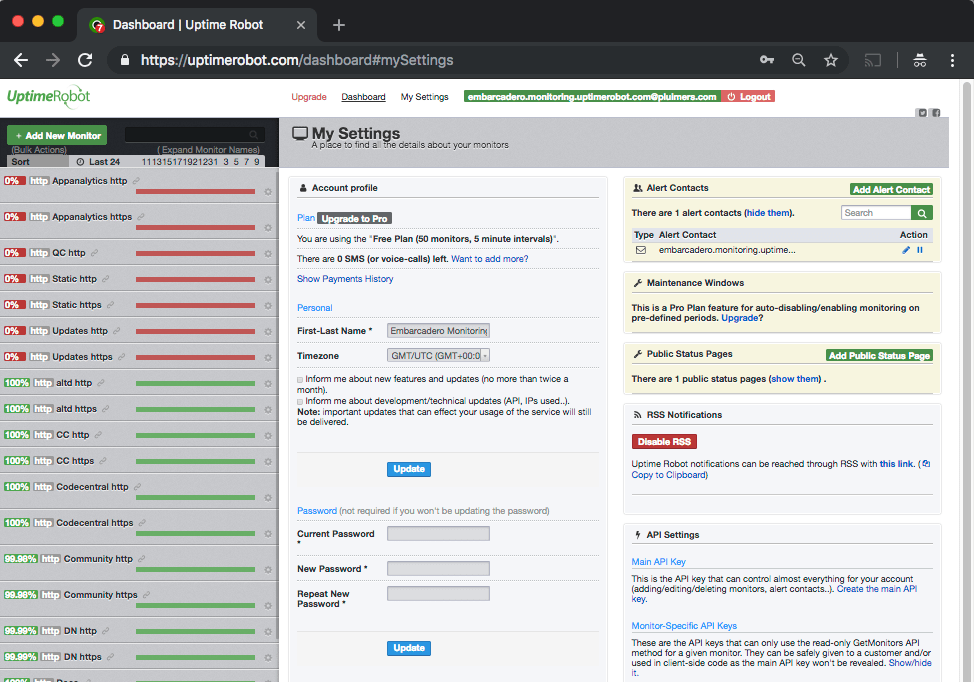
See:
Failing:
Edit 20181205
Found out what happened: the IP got blocked on some spam lists. This is odd:
Even though the SMTP server behind it has relay blocked apart from the 2 domains it is primary MX for, somebody found a trick around it, I think by sending mail to the primary domains that
- are not caught yet by the installed backlist filters
- later bounce when forwarded to their forward address because their blacklist filters are by now more up-to-date,
- then the bounce email being flagged as SPAM.
MXTOOLBOX
The trick caused the IP to appear on 3 blacklists according to MXTOOLBOX:
Checking these revealed all to be around CBL:
CBL:
This IP address was detected and listed 6 times in the past 28 days, and 0 times in the past 24 hours. The most recent detection was at Tue Dec 4 02:25:00 2018 UTC +/- 5 minutes
Your reverse DNS is correct! – snip.xs4all.nl
The IP address for the reverse lookup name matches the original IP – RDNS Information
This is a list from our log files showing the activity from IP address 80.100.143.119. Our system stores information for 4 days.
/ip-log/karma.log.06:black 80.100.143.119 auth-bad ID=79648-15207 X=mxbackup H=snip.xs4all.nl [80.100.143.119]:40353 HELO=[[127.0.0.1]] SN=[M.ASMMSS.06446644586518723606@terrain.gov.harvard.edu] AUTH=[antonio] T=[irena.getheridge2018@outlook.fr] S=[Re: RcPT[(ALERT) | 0644664458]]
Spamhaus ZEN:
80.100.143.119 is not listed in the SBL
80.100.143.119 is not listed in the PBL
80.100.143.119 is listed in the XBL, because it appears in:
dnsbl.spfbl.net
Further research also found an entry in dnsbl.spfbl.net:
Check result of IP 80.100.143.119
This is the rDNS found:
This IP was flagged due to misconfiguration of the e-mail service or the suspicion that there is no MTA at it.
For the delist key can be sent, select the e-mail address responsible for this IP:
- add a PayPal user’s email for 6.00 BRL.
- add a PayPal user’s email for 1.50 USD.
- <abuse@xs4all.nl> qualified.
- <postmaster@snip.xs4all.nl> qualified.
- <postmaster@xs4all.nl> qualified.
The rDNS must be registered under your own domain. We do not accept rDNS with third-party domains.
A chicken-and-egg situation here: since snip.xs4all.nl is blocked because of the blacklist entry, I cannot request a validation email for the blacklist entry.
But then there was MultiRBL showing that most DNS black lists are aggregators of others.
—jeroen
Read the rest of this entry »