Archive for the ‘Security’ Category
Posted by jpluimers on 2023/06/20
Een ontzettend belangrijke podcast is [Wayback/Archive] All the Cyber Ladies – PodcastFeed
Een podcast voor, door en over vrouwen in cybersecurity.
Ik mis geregeld de periode van 30-35 jaar terug waarin IT-teams vaak “gewoon” uit 25% vrouwen bestonden. Gemêleerde teams zijn van onschatbare waarde voor goed functionerende IT, niet alleen vanuit oogpunt van #a11y en #inclusie: ook voor information security.
De tijd maakt inmiddels gelukkig een inhaalslag: er komen steeds meer vrouwen in de IT en je merkt gestaag dat teams diverser worden. All the Cyber Ladies draagt eraan bij dat proces binnen information security verder te versnellen.
De podcast is begin juni dit jaar van start gegaan en heeft nu al een trouwe schare volgers die hopelijk verder groeit naarmate Google deze hoger in de zoek-index opneemt.
Uiteraard is er ook een [Wayback/Archive] All the Cyber Ladies – PodcastFeed RSS zodat je die aan je eigen Podcast Player kunt toevoegen (en vaak staat die er al zoals bijvoorbeeld bij [Wayback/Archive] Player.FM: All The Cyber Ladies podcast)
Via [Wayback/Archive] Lucinda on Twitter: “@jpluimers Zeker!! Je kan de podcast in veel andere players vinden. https://t.co/ksUB8Hd7e4” / Twitter.
–jeroen
Posted in accessibility (a11y), Awareness, Cyber, Development, Inclusion / inclusive society, Infosec (Information Security), Power User, Security, SocialMedia | Leave a Comment »
Posted by jpluimers on 2023/06/08
Many organisations train their personell with phishing attempts from domains that are different from the one the organisation uses.
The mantra is: only respond to emails (or clicking links in them) from domains you know.
Microsoft sent (still sends?) account expiration emails for various *.microsoft.com, *.visualstudio.com and other Microsoft domains like this:
[Wayback/Archive] 232840055-2ccfdb9b-2a13-4a34-92f5-f27f337825f8.png (766×653) email from Microsoft account team <account-security-noreply@mail.msa.msidentity.com>
Read the rest of this entry »
Posted in Pen Testing, Phishing, Power User, Red team, Security | Leave a Comment »
Posted by jpluimers on 2023/05/10
Do not use the Google 2FA Authenticator to to sync secrets across devices.
The why is explained in the (long) tweet by [Wayback/Archive] Mysk on Twitter: “Google has just updated its 2FA Authenticator app and added a much-needed feature: the ability to sync secrets across devices. TL;DR: Don’t turn it on. The new update allows users to sign in with their Google Account and sync 2FA secrets across their iOS and Android devices.…”
For similar reasons, you might not want to use Authy by Twilio to sync between devices either, though that is less insecure as it enforces you to use a backup-password in order to sync these through the cloud: in the past that backup-password had few security restrictions so it was easy to use a relatively insecure password.
Related (most in Dutch):
Read the rest of this entry »
Posted in 2FA/MFA, Authentication, Google, GoogleAuthenticator, Power User, Security | Tagged: 103, 18, 258, 42, securitynl | Leave a Comment »
Posted by jpluimers on 2023/04/26
A less clickbaity title than most articles today as the below only applies to the VMware hypervisors running on MacOS and Windows.
The last Pwn2Own Zero Day Initiative revealed two major issues that allow a virtual machine to either execute code or read hypervisor memory on the VMware Workstation/Player/Fusion host:
- [Wayback/Archive] NVD – CVE-2023-20869
VMware Workstation (17.x) and VMware Fusion (13.x) contain a stack-based buffer-overflow vulnerability that exists in the functionality for sharing host Bluetooth devices with the virtual machine.
- [Wayback/Archive] NVD – CVE-2023-20870
VMware Workstation and Fusion contain an out-of-bounds read vulnerability that exists in the functionality for sharing host Bluetooth devices with the virtual machine.
Both issues have been fixed now, so be sure to deploy the fixes or, if you can’t, apply the workarounds.
Read the rest of this entry »
Posted in Fusion, Power User, Security, Virtualization, VMware, VMware Player, VMware Workstation | Leave a Comment »
Posted by jpluimers on 2023/03/02
Cool: [Wayback/Archive] Canarytokens
Canary tokens are a free, quick, painless way to help defenders discover they’ve been breached (by having attackers announce themselves.)
How tokens works (in 3 short steps):
- Visit the site and get a free token (which could look like an URL or a hostname, depending on your selection.)
- If an attacker ever uses the token somehow, we will give you an out of band (email or sms) notification that it’s been visited.
- As an added bonus, we give you a bunch of hints and tools that increase the likelihood of an attacker tripping on a canary token.
The above documentation is just a small portion of what is at [Wayback/Archive] Canarytokens.org – Quick, Free, Detection for the Masses with even more documentation starting at [Wayback/Archive] Introduction | Canarytokens.
Source code (either the site or a docker image):
It is provided by [Wayback/Archive] Thinkst Canary.
I learned it at the height of the Log4Shell mitigation stress. Some related posts from that period:
Via: [Archive] ᖇ⦿ᖘ Gonggrijp on Twitter: “IP in Luxembourg, owned by Frantech Solutions from Cheyenne, WY. Judging from a quick round of Google appears to be a bulletproof VM hoster, with clients to match. ” / Twitter

Below image via [Wayback/Archive] Tweet2Img.com | Perfect Tweet screenshots with just one click

––jeroen
Posted in Power User, Security | Leave a Comment »
Posted by jpluimers on 2023/02/04
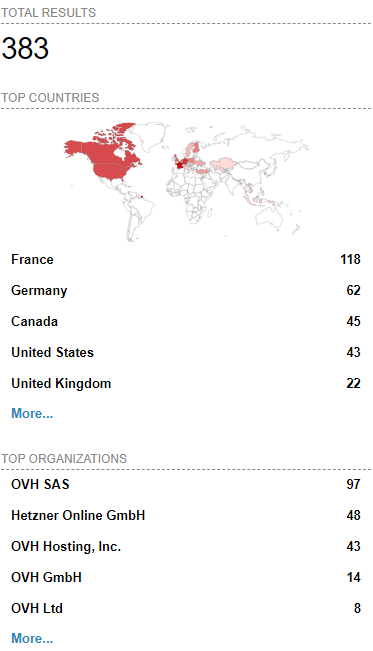
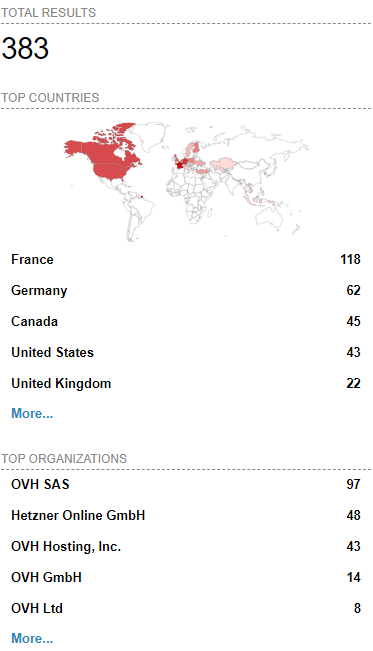 [Wayback/Archive] Massive ESXiArgs ransomware attack targets VMware ESXi servers worldwide
[Wayback/Archive] Massive ESXiArgs ransomware attack targets VMware ESXi servers worldwide
Admins, hosting providers, and the French Computer Emergency Response Team (CERT-FR) warn that attackers actively target VMware ESXi servers unpatched against a two-year-old remote code execution vulnerability to deploy ransomware.
Tracked as
CVE-2021-21974, the security flaw is caused by a heap overflow issue in the OpenSLP service that can be exploited by unauthenticated threat actors in low-complexity attacks.
“As current investigations, these attack campaigns appear to be exploiting the vulnerability CVE-2021-21974, for which a patch has been available since 23 February 2021,” CERT-FR said.
“The systems currently targeted would be ESXi hypervisors in version 6.x and prior to 6.7.”
To block incoming attacks, admins have to disable the vulnerable Service Location Protocol (SLP) service on ESXi hypervisors that haven’t yet been updated.
CERT-FR strongly recommends applying the patch as soon as possible but adds that systems left unpatched should also be scanned to look for signs of compromise.
CVE-2021-21974 affects the following systems:
- ESXi versions 7.x prior to ESXi70U1c-17325551
- ESXi versions 6.7.x prior to ESXi670-202102401-SG
- ESXi versions 6.5.x prior to ESXi650-202102101-SG
[Wayback/Archive] Esxi Ransomware Help and Support Topic (ESXiArgs / .args extension) – Page 2 – Ransomware Help & Tech Support (there are now 4 pages, most victims OVH, likely many more pages to follow)
[Wayback/Archive] How to Disable/Enable the SLP Service on VMware ESXi (76372)
[Wayback/Archive] html:”We hacked your company successfully” title:”How to Restore Your Files” – Shodan Search which resulted in the above image (I tweeted it at [Wayback/Archive] Jeroen Wiert Pluimers @wiert@mastodon.social on Twitter: “@vmiss33”)
Commands used in [Wayback/Archive] Jeroen Wiert Pluimers @wiert@mastodon.social on Twitter: “@vmiss33 I did forget to disable SLP on a patched system, but doing that is easy as per kb.vmware.com/s/article/76372“:
/etc/init.d/slpd status
/etc/init.d/slpd stop
esxcli system slp stats get
esxcli network firewall ruleset set -r CIMSLP -e 0
chkconfig slpd off
chkconfig --list | grep slpd
More links to follow, but I’m away from keyboard for most of the day.
–jeroen
Read the rest of this entry »
Posted in ESXi6, ESXi6.5, ESXi6.7, Power User, Ransomware, Security, Virtualization, VMware, VMware ESXi | Leave a Comment »
Posted by jpluimers on 2022/11/28
I wish they had mailed me about this: [Wayback/Archive] De Non-Mailing-Indicator
Als je na je inschrijving in het Handelsregister niet benaderd wilt worden met fysieke post of huis-aan-huis bezoek op je ingeschreven adres, dan kun je de NMI activeren. Hiermee geef je aan dat je geen ongevraagde reclame per post of verkoop aan je deur wilt.
Na het activeren van de NMI staat dit zowel op het uittreksel als in de gratis toegankelijke informatie op de website.
…
De bescherming die de NMI biedt, is beperkt tot fysieke post en huis-aan-huis bezoek. De NMI beschermt niet tegen reclame en aanbiedingen via e-mail, telefoon, sms of WhatsApp. Je moet er rekening mee houden dat je ondanks de activering snel na je inschrijving benaderd gaat worden met allerlei aanbiedingen. Bedrijven en organisaties maken daarvoor gebruik van de openbare gegevens van het Handelsregister.
…
Het aanzetten van de NMI betekent dat je minder goed gevonden wordt. Zo heeft Google als beleid dat ze bedrijven met een NMI niet opneemt in Google Maps.
…
Je kunt eenvoudig via een formulier de [Wayback/Archive] Non-Mailing-Indicator activeren of deactiveren.
Met dit formulier kun je de non-mailing-indicator (NMI) activeren of deactiveren. Kies je voor ‘activeren’ dan mogen jouw gegevens uit het Handelsregister niet worden gebruikt voor postreclame of verkoop aan de deur. Je kunt zelf checken of je de NMI wel of niet hebt geactiveerd. Doe hiervoor de volgende stappen:
- Ga naar [Wayback/Archive] de bedrijvenzoeker en vul je bedrijfsnaam of KVK-nummer in.
- Klik op jouw bedrijfsnaam. Je gaat nu naar een pagina waar alle gegevens van jouw bedrijf staan.
- Zie jij de zin “De onderneming/organisatie wil niet dat haar adresgegevens worden gebruikt voor ongevraagde postreclame en verkoop aan de deur” staan? Dan heb jij je NMI geactiveerd. Zie je deze zin niet, dan heb jij de NMI niet geactiveerd.
Als je je inschrijft in het Handelsregister kun je direct de NMI activeren. Als je de NMI op een later tijdstip activeert, bijvoorbeeld enkele maanden na je inschrijving, dan zijn je gegevens al bij veel bedrijven en organisaties bekend en opgenomen in hun databestanden. Dit wordt niet automatisch aangepast tenzij deze bedrijven regelmatig via KVK een update aanvragen. Omdat het achteraf activeren van de NMI in de praktijk weinig effect blijkt te hebben, kun je er het beste voor kiezen om dat meteen bij de inschrijving te doen.
––jeroen
Posted in About, LifeHacker, Personal, Power User, Security | Leave a Comment »
Posted by jpluimers on 2022/10/19
Posted in Development, FortiGate/FortiClient, Hardware, Network-and-equipment, Power User, Security, Software Development, VPN, Windows, Windows 10, Windows 7, Windows 8, Windows 8.1, Windows 9, Windows Development, Windows Server 2000, Windows Server 2003, Windows Server 2003 R2, Windows Server 2008, Windows Server 2008 R2, Windows Server 2012, Windows Server 2012 R2, Windows Server 2016, Windows Vista, Windows XP | Leave a Comment »









 [
[